Ransomware attacks are everywhere these days, it’s the number one cyber threat that organizations face and a major risk for their business, and this isn’t going to change any time soon.
While helping companies to prepare for and recover from these ransomware attacks, we are seeing an evolution in extortion techniques that could change the odds in favor of the criminals.
Encrypting your files is still the initial tactic. Attackers gain access to your network, encrypt your documents, systems, and backups, hereby making your IT systems and data unusable, and ask for a ransom to get the decryption key that will unlock your files. This is the classical ransomware attack where we have written about before.
With more companies investing in protective technologies such as tamper-proof backup solutions that make it possible for them to recover from a ransomware attack without paying the ransom, attackers are moving into new extortion techniques to protect their criminal revenues.
Stealing your data
Today, many hacking groups will – before they encrypt your systems – copy and exfiltrate your data such as intellectual property, sensitive personal data, customer and supplier information, etc… With the stolen data, attackers can threaten to release all data to the public or offer it for sale on underground markets unless the victim pays the ransom to ‘buy back’ its own data.
Some of these criminals will also threaten to release fake press announcements from the company under attack about the on-going ransomware incident and associated data-loss, and – especially in Europe – to inform the data protection authorities. They will scare the victim into paying the ransom or otherwise face heavy financial sanctions by these authorities.
The more advanced hacking groups usually use dedicated sites where they publish these leaks, but often attackers also use underground forums for this.
The problem with this type of extortion is that even if you pay the ransom to avoid this from happening, there is no guarantee that all your data will be destroyed, won’t be resold, or won’t be leaked by the criminals anyway. There have been cases where the ransom had been paid but the data was leaked nevertheless or where the company were re-extorted for the same stolen data-set weeks after the ransom was paid.
Contacting your customers, partners, and employees
If the previous tactics did not yield results, some attackers will go beyond the initial victim by contacting current and former employees, customers and suppliers to put even more pressure on the victim to pay the requested ransom.
Attackers attempt to offer customers and suppliers to buy all of the victim’s stolen data or only the data that involves the recipient, including some sample documents as proof that it’s not an empty offer.
In emails to current and former employees, people are offered the opportunity to get access to the victim’s sensitive data such as the company’s salary data, or to buy back their personal sensitive data.
In a rare case, attackers even abused employees’ personal accounts and passwords that were obtained during the attack to exercise pressure.
This approach puts a lot of extra stress on a company whose business is still impacted by the initial ransomware attack. Suddenly, the company’s entire eco-system is starting to ask questions about what happened, whether the company had weak cyber security, what data was impacted and why was some of the stolen data still on the victim’s systems. This has a psychological and reputational impact, not only on the people that are dealing with the incident but also on the entire staff, customers, and partners.
Executing a Distributed Denial-of-Service (DDoS)
When you manage to recover from a ransomware attack without paying the ransom, some attackers will try to keep you from going online by executing a DDoS attack on your internet services or will threaten with this type of attack if the ransom isn’t paid.
A DDoS is an attack where your internet services are flooded with traffic from different sources, effectively making your services unavailable to normal customers.
This type of extortion is also used by some cybercriminals as a stand-alone attack, especially targeting companies that rely on internet facing services during a specific timeframe to do business. Imagine for example a company that’s live streaming a sports event, or a payment provider during the Christmas shopping period that is being threatened with a DDoS attack during the timeframe they need their service to be up-and-running the most.
Avoid the worst, be prepared
What can you do as an organization to be better prepared against these ransom attacks?
Detect the attack before exfiltration starts
Executing a ransomware attack is a step-by-step approach that typically takes some time before the victim is being asked for ransom, especially when criminals want to exfiltrate your data first. Hence, the crux is in early spotting and stopping their criminal actions before they start exfiltrating and encrypting your data. As always within cybersecurity, prevention is ideal but early detection and rapid response are a must.
Assess your current preparedness with a ransomware tabletop simulation
In our experience, a tabletop simulation with the broader management team that goes beyond IT will help you uncover gaps in your current crisis management processes, your defenses and preparedness from a business perspective such as internal and external communication, legal, HR, etc. This will also help you determine which IT assets are critical for your business and might be at risk during such an attack. When you also would be operating Operational Technology (OT) environments such as manufacturing plants, utilities, transport that are typically blind spots for the IT department, it is important to include these in the scope of your simulation.
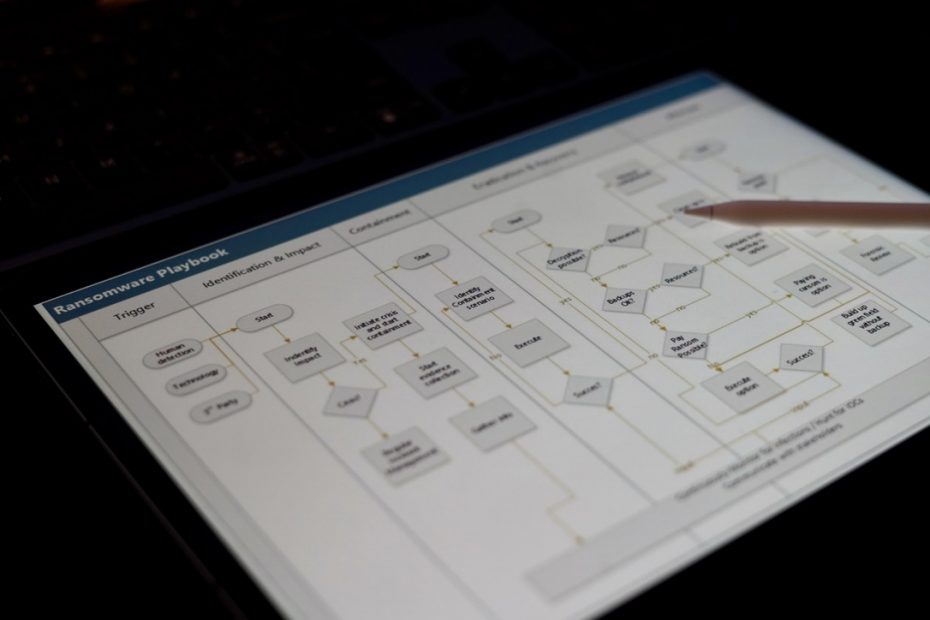
Develop a playbook for ransomware attacks
A playbook will serve as a guide to the organization on what to do in case of a ransomware incident. Preparing this up front will help facilitating the decision-making process during a crisis so that you don’t lose time thinking about various options during the crisis.
A playbook should detail how to detect, who to involve, the decisions to be made, and the actions to be taken based on the characteristics of the attack. It should contain not only IT/technical measures and actions, but it should also include a communication strategy on how to deal with internal and external stakeholders, when to ask for legal input and advice, when to notify authorities etc. The communication with your staff, customers and suppliers will take away a lot of your precious time not only during but also after the incident, so you should be well prepared for it.
Developing this will also help you identify the gaps still present in your preparedness for a ransomware incident and can help define an action plan to bridge these gaps. We can help you identifying your cybersecurity needs and developing the playbook.
Practice your playbook
Having a playbook is one thing, executing it during a crisis is another. To make sure that everyone in the organization knows what is expected from them in case of a ransomware attack, it is crucial to train and test your playbook regularly. Tabletop exercises will help you uncover gaps in your playbook and help everyone involved to better understand what is expected from them. We have extensive experience in delivering these tabletop exercises and can provide these entirely tailored to your needs and target audience.
Don’t hang on to data
Specifically with respect to the attackers’ extortion methods of stealing data and contacting your stakeholders as described above, it is key that you don’t have more data on your systems than you need to run your business:
- Make sure to implement and enforce data protection and data lifecycle policies to discard data that is no longer needed safely.
- Create an inventory of contractual requirements you have with respect to protection and removal of data. This will also help you to better understand what your obligations and liabilities are towards your partners and customers when their data would be exposed or impacted by a cyberattack.
- Leverage the efforts you have done in the scope of compliance with the EU General Data Protection Regulation (GDPR) to understand what personal data you are processing and what is expected from you if personal data gets impacted from a ransomware attack.
Are you unsure how well you are prepared for these new types of ransom attacks, and would like to have help preparing and setting up your cyber incident response capability? Don’t hesitate to get in touch!
We can also help you with defining and rolling-out your cybersecurity strategy for both IT and OT, performing security and gap assessments, and procuring and implementing the right security services for your needs.